Les Bell
Blog entry by Les Bell
Welcome to the first of what I hope will be many weekly news briefs. This is a short one, starting part-way through the week, and consists of the stories that cross my desk as I continually update the various course wikis.
News Stories
Data Breach Costs Now Average $US4.35 Million
The cost of a data breach can be significant and continues to rise each year, hitting an average of $US4.35 million in the year between March 2021 and March 2022 (Fowler, 2022; Ponemon Institute and IBM Security, 2022). Critical infrastructure operators face even higher costs, with an average breach costing $US4.82 million.
Of the 550 organizations who responded to the Ponemon/IBM Security Cost of a Data Breach study, 83% had had more than one breach. 45% of the breaches were cloud-based, while 19% occurred because of a compromise at a business partner. There's more info for course attendees in the Cyber Event Impact and Asset Valuation pages of the CISSP Fast Track Review course wiki.
Fowler, Bree, Average Data Breach Costs Hit a Record $4.4 Million, Report Says, CNet, 27 July 2022. Available online at https://www.cnet.com/tech/services-and-software/average-data-breach-costs-hit-a-record-4-4-million-report-says/.
Ponemon Institute and IBM Security, Cost of a Data Breach Report 2022, IBM Security technical report, July 2022. Available online at https://www.ibm.com/security/data-breach.
Fraudulent Crypto Apps Net $US42.7 Million
The FBI has warned that cyber criminals are contacting investors and convincing them to download fraudulent mobile apps for cryptocurrency services. To date, 244 victims have been identified, with a collective total loss of $US42.7 million (Federal Bureau of Investigation, 2022). Investors are warned to be wary of unsolicited requests to download investment applications, verify that the company offering the app is legitimate, and treat applications with limited and/or broken functionality with skepticism.
In a letter to Apple CEO Tim Cook and Google CEO Sundar Pinchai, US Senator Sherrod Brown transferred some liability to the tech firms, asking them to explain their processes for reviewing and approving crypto trading and wallet apps in their app stores (Kelly, 2022). Meanwhile, multiple US government agencies are pursuing alleged crypto scammers (Clark, 2022).
The CISSP course wiki page on Cryptocurrencies and Blockchain Technology contains more detail.
Clark, Mitchell, The government's going after alleged crypto scammers as market crashes, The Verge, 1 July 2022. Available online at https://www.theverge.com/2022/7/1/23188158/government-actions-cftc-doj-fbi-bitcoin-nft-investment-scams-market-crash.
Federal Bureau of Investigation, Cyber Criminals Create Fraudulent Cryprocurrency Investment Applications to Defruad US Investors, FBI Cyber Division Private Industry Notification, 18 July 2022. Available online at https://www.ic3.gov/Media/News/2022/220718.pdf.
Kelly, Makena, Apple and Google come under scrutiny for scammy crypto apps, The Verge, 28 July 2022. Available online at https://www.theverge.com/2022/7/28/23282297/apple-google-cryptocurrency-app-scams-trading-investors-senate.
UEFI Rootkits Discovered After 6 Years in the Wild
The UEFI BIOS flash ROM of system boards offers a particularly effective hiding place for rootkits - specifically, bootkits which infect a system before the operating system boots and loads - and which can survive reinstallation of the operating system and applications or even complete replacement of an SSD or hard drive.
In 2016, security firm Qihoo 360 reported on an early UEFI rootkit which had existed for a year, but the Western world did not notice this. However, Kaspersky has now detailed how the rootkit - which can reside in the firmware of some Gigabyte and ASUS motherboards - hijacks the boot process, acting to modify the boot manager, then the OS loader, the OS kernel and finally contacts a C2 server to download a malware payload (Global Response and Analysis Team, 2022).
The bootkit appears to be of Chinese origin, and has been detected in China, Vietnam, Iran and Russia. Some components of the bootkit chain have previously been used by a Chinese-operated botnet called MyKings (Goodin, 2022). You can find more information in the Rootkits and Memory pages of the CISSP course wiki.
Goodin, Dan, Discovery of new UEFI rootkit exposes an ugly truth: The attacks are invisible to us, Ars Technica, 27 July 2022. Available online at https://arstechnica.com/information-technology/2022/07/researchers-unpack-unkillable-uefi-rootkit-that-survives-os-reinstalls/.
Global Response and Analysis Team, CosmicStrand: the discovery of a sophisticated UEFI firmware rootkit, Kaspersky SecureList, 25 July 2022. Available online at https://securelist.com/cosmicstrand-uefi-firmware-rootkit/106973/.
Malicious Browser Extension Steals Emails
A malicious extension for Chromium-based web browsers (Chrome, Edge and Whale) can install invisibly to the user and then steal emails from GMail and AOL accounts (Gatlan, 2022). The attackers, believed to be a North Korean group dubbed Kimusky, and previously the subject of a CISA alert in 2020, install the extension by using a VBS script to replace the browsers preferences and secure preferences files with ones downloaded from a C2 server. Once the files have been replaced, the browser will automatically install the extension, which inspects and infiltrates emails. Kimusky targets victims working in foreign policy, nuclear and other areas of strategic interest, primarily in the US, Europe and South Korea. There is more information for course attendees in the Browser Attacks page of the CISSP course wiki.
Cybersecurity & Infrastructure Security Agency, North Korean Advanced Persistent Threat Focus: Kimusky, Alert AA20-301A, 27 October 2020. Available online at https://www.cisa.gov/uscert/ncas/alerts/aa20-301a.
Gatlan, Sergiu, Cyberspies use Google Chrome extension to steal emails undetected, Bleeping Computer, 28 July 2022. Available online at https://www.bleepingcomputer.com/news/security/cyberspies-use-google-chrome-extension-to-steal-emails-undetected/.
Cyber Mercenary Sells Windows and Adobe Zero-Day Exploits
Although many APT's are either directly employed by, or at least sponsored by, nation states and occasionally terrorist networks, there are mercenary black hats who develop and sell zero-day exploits. One example, identified by Microsoft, seems to be selling Windows and Adobe Reader zero-day exploits to customers who have used them to target law firms, banks and strategic consultancies in the UK, Austria and Panama (Lakshamanan, 2022). The attacker, which Microsoft refers to as KNOTWEED, also acts directly, offering access-as-a-service and hack-for-hire services. Read more about Advanced Persistent Threats in the CISSP course wiki.
Lakshamanan, Ravie, Microsoft Uncovers Austrian Company Exploiting Windows and Adobe Zero-Day Exploits, The Hacker News, 28 July 2022. Available online at https://thehackernews.com/2022/07/microsoft-uncover-austrian-company.html.
Samsung Feature Protects Personal Data from Phone Technicians
Samsung is preparing to introduce a new feature for their Galaxy phones which will protect personal data from technicians working to repair a phone (Amadeo, 2022). Before sending a phone for repair, the owner can put the phone in 'repair mode'; technicans can now work on the phone and will have access to the default apps, but with no personal data, so that they can test the phone's operation. Upon return, the owner can re-authenticate, turn off 'repair mode' and resume normal usage.
Although Samsung does not reveal how the feature works, it is quite probably based on standard functionality of the underlying Android operating system, such as user profiles. Expect similar functionality from other phone manufacturers in the future.
Amadeo, Ron, Samsung's "repair mode" lets technicians look at your phone, not your data, Ars Technica, 30 July 2022. Available online at https://arstechnica.com/gadgets/2022/07/samsungs-repair-mode-lets-technicians-look-at-your-phone-not-your-data/.
Australian Spyware Author Charged
The Australian Federal Police have charged a 24-year-old Frankston man with six offences for creating, selling and administering a remote access tool between 2013 and 2019. The man had sold his RAT, which was named Imminent Monitor, to more than 14,500 people in 128 countries and had netted somewhere between $A300,000 and $A400,000 from the malware, which he mostly spent on delivery of fast food and other consumable items.
The AFP identified some 200 purchasers in Australia, mostly through their PayPal records, and also identified 44 victims; 14 of the purchasers had domestic violence orders against them and one was also registered on the Child Sex Offender Register. Global police raids in June 2019 resulted in 13 people being arrested for criminal activity using the RAT.
There is more information on trojan programs in the CISSP course wiki.
Travers, Penny and Elizabeth Byrne, Australian man charged over alleged spyware operation after global investigation involving AFP, ABC News, 30 July 2022. Available online at https://www.abc.net.au/news/2022-07-30/afp-charge-australian-man-over-alleged-spyware-operation/100996670.
Byrne, Elizabeth, AFP charge Australian man over alleged spyware operation, ABC TV News, 29 July 2022. Available online at https://www.youtube.com/watch?v=KtdfN06ur2s.
Hackers Work Around Disabling of MS Office Macros
While Microsoft has disabled the automatic execution of macros in its Office suite, threat actors have simply adopted a variety of new techniques to work around this. Between October 2021 and June 2022 the use of macro-enabled attachments by attackers dropped by about 66%, but they simply switched to using ISO, ZIP, RAR and other container attachments, as well as Windows Shortcut (.lnk) files. The reason for this is that Windows flags downloaded files as untrusted, with an attribute called the Mark of the Web (MOTW). So a directly downloaded .xlsx file will bear the Mark of the Web. A downloaded ZIP file will also bear the MOTW - but a spreadsheet file extracted from it will not. Attackers are also increasing their use of .XLL files, a specialized type of .DLL (Dynamic Link Library) file for Excel.
Larson, Selena, Daniel Blackford and the Proofpoint Threat Research Team, How Threat Actors Are Adapting to a Post-Macro World, Proofpoint blog, 28 July 2022. Available online at https://www.proofpoint.com/us/blog/threat-insight/how-threat-actors-are-adapting-post-macro-world.
Supply Chain Security Guidelines, In Brief
Back in May, NIST released an update to SP 800-161, "Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations". The 326-page document is dense, as you'd expect, but IBM's Security Intelligence blog has a useful summary (Elgan, 2022).
Elgan, Mike, NIST Supply Chain Security Guidelines: 10 Key Takeaways, IBM Security Intelligence, 28 July 2022. Available online at https://securityintelligence.com/articles/nist-supply-chain-guidelines-ten-takeaways/. There's more info in our CISSP Fast Track Review course wiki page on Cybersecurity Supply Chain Risk Management, obviously (for those enrolled in the course only).
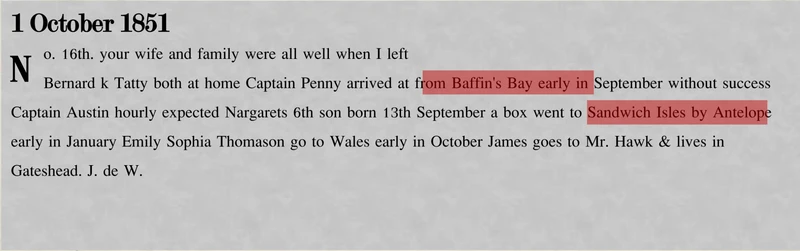
Codebreakers Finally Break Some 1850's Ciphertext
This is absolutely fascinating. Between 1850 and 1855, a series of cryptic advertisements appeared in newspaper, The Times. Over the decades, many attempts were made to break and read these, but were always unsuccessful.
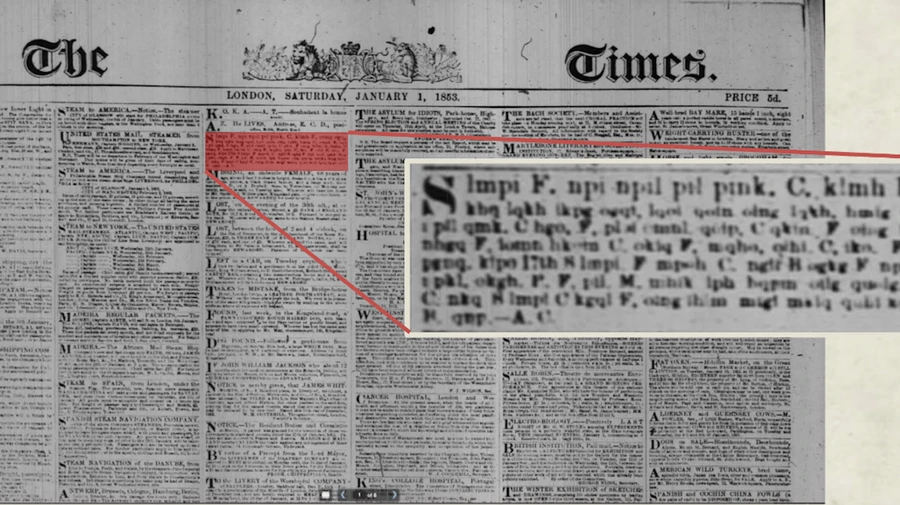
The ad appearances coincided with an attempted rescue mission headed by naval officer Richard Collinson, who was trying to find lost arctic explorer John Franklin and his men, who had disappeared in 1848. Franklin had set out to find the fabled Northwest Passage which would link the Atlantic and Pacific Oceans via the north of Canada, speeding trade with Asia and India.
Cryptanalysts Elonka Dunin and Klaus Schmeh, aided by journalist A.J. Jacobs, tackled the mystery, and have now cracked some of the ads with the aid of an 1817 naval codebook.
You can read the full story here:
Franceschi-Biccierai, Lorenzo, Codebreakers Find 'Sexts', Arctic Dispatches in 200-Year-Old Encrypted Newspaper Ads, Vice Motherboard, 27 July 2022. Available online at https://www.vice.com/en/article/4axwz3/codebreakers-find-sexts-arctic-dispatches-in-200-year-old-encrypted-newspaper-ads.
Free Online Skills Courses
Recruitment and personnel management company Hays has been promoting free courses, some of which may be useful to technical professionals. A few relevant topics include:
- Implementing a Digital Transition
- Defining Problems Accurately
- Understanding Communication Skills
- What is Design Thinking?
- Root-Cause Analysis to Solve Problems
- Ethical Hacking (!?!)
I have not investigated these, cannot testify to their quality, and offer no warranties - it's possible that after registering, you are bombarded with marketing materials, and if you are, please let me know.
See https://www.hays.com.au/online-learning/skills-development.
Site News
New Forums
Attendees at our courses now have access to three new forums which allow for social chat, job-related postings (both recruiting and job-seeking) and services (again, both looking for and providing services such as pen-testing, consulting, audits, mentoring, etc.). These are located in the Security Watering Hole, where we can safely congregate.