Les Bell
Blog entry by Les Bell
Welcome to today's daily briefing on security news relevant to our CISSP (and other) courses. Links within stories may lead to further details in the course notes of some of our courses, and will only be accessible if you are enrolled in the corresponding course - this is a shallow ploy to encourage ongoing study. However, each item ends with a link to the original source.
News Stories
More Analysis of BEC Attacks
Over the last couple of days, we have covered business email compromise attacks, and today provides yet another example. This time, Israeli incident response firm Sygnia provides an analysis of a BEC campaign affecting dozens of victim organizations world-wide.
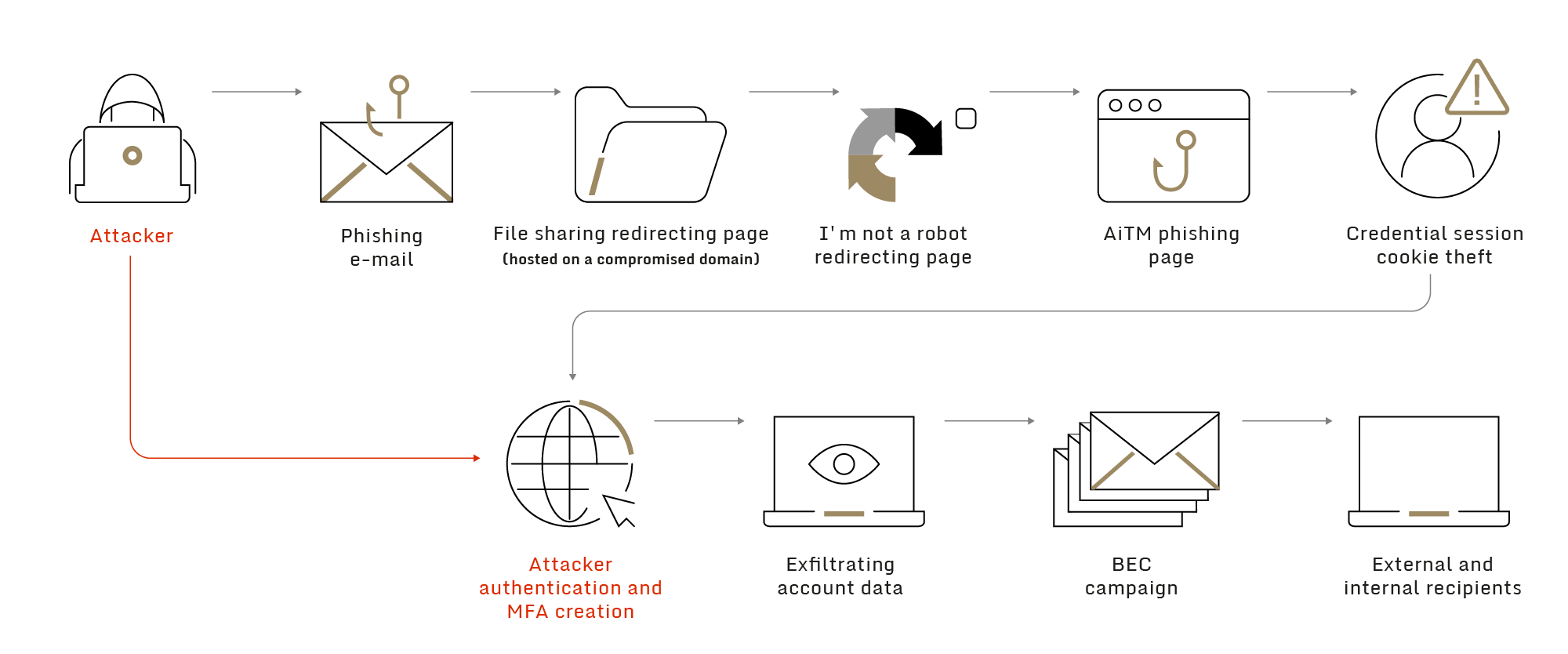
High-level description of the attack chain (image credit: Sygnia)
Their analysis, produced using an array of threat intelligence tools, shows the following steps:
- A phishing email was sent to one of Sygnia's client’s employees, originating from a legitimate mailbox of an external company, assumed to be previously compromised.
- The phishing email included a link leading to a file sharing request page, hosted on an assumed to be compromised domain, with a URL path associated with the email sender’s company.
- Upon clicking the link, the victim was referred to an ‘I'm not a robot’ check hosted by Cloudflare, which acts as an anti-tracing method.
- After passing the check, the victim was referred to a fraudulent Office365 authentication page, generated by a phishing kit.
- After the victim entered his credentials, the phishing kit initiated an ‘Adversary in The Middle’ (AiTM) attack, forwarding the client authentication and MFA challenge to a legitimate Microsoft authentication service while stealing the acquired session token as well as the credentials to enable access to the account.
- The threat actor then logged into the victim’s account using the stolen token and added a new MFA device to gain persistent access.
- Once persistent access was achieved, the threat actor created a new file sharing request site related to the new victim’s company and compromised account.
- In addition to exfiltration of sensitive data from the compromised account, the threat actor used this access to send new phishing emails containing the new malicious link to dozens of the client’s employees as well as to additional targeted organizations.
These tactics are similar to those analyzed by MicrosoftThreat Intelligence, which we reported on yesterday. The value of Cygnia's report is its detailed demonstration of analytic pivoting and the variety of tools used. The implications for likely victims are clear: use of multi-factor authentication is not much of a defense when poorly-trained and unaware users can fall victim to Man-in-the-Middle attacks.
Sadon, Amir, Dor Fenigshtein, Shani Adir Nissim, Amnon Kushni and Ori Porag, Case Study: cracking a global Adversary-In-The-Middle campaign using a threat intelligence toolkit, blog post, 13 June 2023. Available online at https://blog.sygnia.co/cracking-global-phishing-campaign-using-threat-intelligence-toolkit.
Chinese APT Exploits ESXi 0day
Last year, Mandiant reported on a new technique which was being used by UNC3886, a possibly Chinese cyber-espionage threat actor (the UNC designation means that the actor was as yet uncategorized). The technique involved the creation of malicious vSphere Installation Bundles (VIB's) and duping the ESXi server into installing them by faking the acceptance level of the bundle.
By default, a ESXi host will only install bundles with an acceptance level of PartnerSupported or above; in this case, the attacker had modified the bundle's XML descriptor, changing the acceptance-level field from Community-Supported to PartnerSupported, and while this meant that the digital signature of the bundle would not validate, the attacker simply removed the signature and used the --force or --no-sig-check options on the installation command to get the bundle installed anyway.
This technique was used to install backdoors on the ESXi servers, executing commands on guest machines through the vmtoolsd.exe process, from which information, including credentials, could then be exfiltrated.
Now UNC3886 is back, with additional techniques. Their primary goal seems to be to evade detection; this may be why they target VMware ESXi hosts in the first place, since they commonly do not support EDR products. The evasion techniques mployed by this actor include:
- Harvesting credentials for service accounts from a vCenter Server for all connected ESXi hosts from the embedded vPostgreSQL server built into vCenter Server Appliance
- Exploiting a zero-day vulnerability (CVE-2023-20867) that enabled the execution of privileged commands across Windows, Linux, and PhotonOS (vCenter) guest VMs without authentication of guest credentials from a compromised ESXi host and no default logging on guest VMs
- Deploying backdoors on ESXi hosts using an alternative socket address family, VMCI, for lateral movement and continued persistence. This address family enabled direct reconnection from any guest VM to the compromised ESXi host’s backdoor regardless of network segmentation or firewall rules in place.
- Continuing to tamper with and disable logging services on impacted systems, presenting additional challenges to investigating UNC3886 in a compromised environment.
An interesting point about this report is IOC's reported: following previous Mandiant reports, UNC3886 has been very quick to change the atomic IOC's of its tools, such as file names and digests. Accordingly, this time Mandiant has focused on the tactics and methodologies used by the group - in effect, behvioural IOC's.
Marvi, Alexander, Jeremy Koppen, Tufail Ahmed, Jonathan Lepore, Bad VIB(E)s Part One: Investigating Novel Malware Persistence Within ESXi Hypervisors, blog post, 28 September 2022. Available online at https://www.mandiant.com/resources/blog/esxi-hypervisors-malware-persistence.
Marvi, Alexander, Brad Slaybaugh, Ron Craft and Rufus Brown, VMware ESXi Zero-Day Used by Chinese Espionage Actor to Perform Privileged Guest Operations on Compromised Hypervisors, blog post, 13 June 2023. Available online at https://www.mandiant.com/resources/blog/vmware-esxi-zero-day-bypass.
DoJ Scores Two Wins
The US Attorney's Office, Southern District of New York, has scored a couple of small victories in the last few days.
First, along with the Northen District of Califironia and the DoJ's Criminal Division, it laid charges against two Russian nationals for their part in the 2011 theft of cryptocurrency from wallets on the Mt. Gox exchange, which ultimately led to its collapse in 2014. Alexey Bilyuchenko, 43, and Aleksandr Verner, 29, are accused of conspiring to launder approximately 647,000 bitcoins from the 2011 hack.
Bilyuchenko is separately charged in the Northern District of California with conspiring with Alexander Vinnik to operate the illicit cryptocurrency exchange BTC-e from 2011 to 2017, laundering funds for cybercriminals worldwide.
Of course, indictment is one thing; both Bilyuchenko and Verner remain at large, probably in Russia, making their appearance in court unlikely.
In a separate case, Mihai, Ionut Paunescu, a.k.a "Virus", was sentenced to three years in prison for conspiracy to commit computer intrusion in connection with running a “bulletproof hosting” service that enabled cybercriminals to distribute the Gozi Virus, the Zeus Trojan, the SpyEye Trojan, and the BlackEnergy banking trojans. Paunesco had also been involved in DDoS attacks and spamming, and had pleaded guilty back in February.
Biase, Nicholas, Russian Nationals Charged With Hacking One Cryptocurrency Exchange And Illicitly Operating Another, press release, 9 June 2023. Available online at https://www.justice.gov/usao-sdny/pr/russian-nationals-charged-hacking-one-cryptocurrency-exchange-and-illicitly-operating.
Biase, Nicholas, Romanian National Who Operated “Bulletproof Hosting” Service That Facilitated The Distribution Of Destructive Malware Sentenced To Three Years In Prison, press release, 12 June 2023. Available online at https://www.justice.gov/usao-sdny/pr/romanian-national-who-operated-bulletproof-hosting-service-facilitated-distribution.
These news brief blog articles are collected at https://www.lesbell.com.au/blog/index.php?courseid=1. If you would prefer an RSS feed for your reader, the feed can be found at https://www.lesbell.com.au/rss/file.php/1/dd977d83ae51998b0b79799c822ac0a1/blog/user/3/rss.xml.
![]()
 Copyright to linked articles is held by their individual authors or publishers. Our commentary is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License and is labeled TLP:CLEAR.
Copyright to linked articles is held by their individual authors or publishers. Our commentary is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License and is labeled TLP:CLEAR.